There are days when I feel like throwing up my hands and declaring the phrase ‘Internet security’ to be an oxymoron, like ‘unbiased opinion’, ‘exact estimate’ and the classic ‘military intelligence’. The problem IT professionals are faced with is not a dearth of good security solutions, but the constant evolution of risk. Using the Internet these days is a bit like travelling: it’s a good idea to hide your valuables, preferably under many layers of clothing. Similarly, but on the enterprise level, I recommend layers of Internet security – including VPN tunnels – as the best current way to keep your mission-critical data and networks safe from malicious parties.
Why Layers?
A layered security strategy is, in my opinion, essential. My favorite way of explaining the layered approach is by way of the ‘Swiss cheese’ model. Imagine that each separate layer of security is a slice of Swiss cheese, a barrier to entry, with the occasional hole. One slice may protect you from some intruders, but it’s not going to help against the clever or persistent. So, you add another slice. Now most of the holes in the first piece of cheese are covered. Again, this isn’t going to protect you forever, but it’s a ‘hole’ lot better than it was. Add another slice, and another, and another, and the time, energy and resources criminals’ need to successfully attack you mount up. If there’s enough cheese (I mean layers of security) between you and your attackers, they are likely to look for a less secure target.
As we’ll discover later on, a VPN network actually adds several slices of cheese (I mean layers of security) all on its own.
What is a VPN?
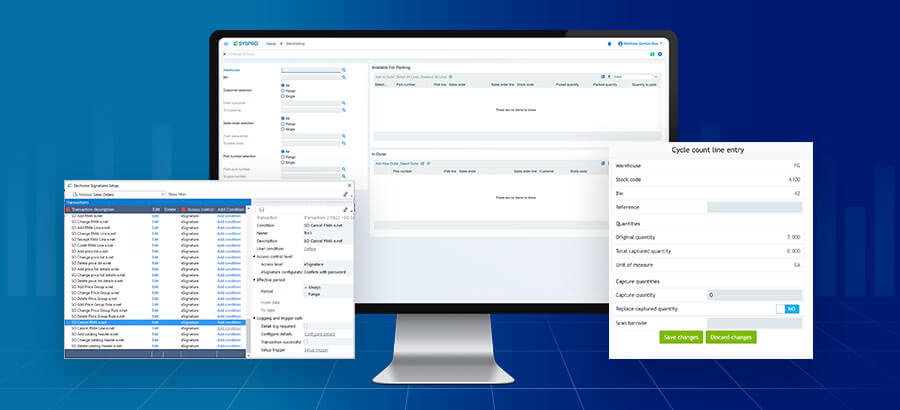
A Virtual Private Network (VPN) provides organizations with a way of protecting transmitted information over a shared or public network, such as the Internet. It does this by enabling users to establish a virtual private ‘tunnel’ between two networks, allowing remote access to the company Local Area Network (LAN), along with its resources, data and communications. Connecting to a VPN network has the effect of being connected to resources on a distant network, say Sydney, from [almost*] anywhere in the world and having something like a LAN experience while in New York. By using a VPN, an enterprise can extend the reach of its LAN (and thus its ERP) without recourse to leased lines such as T1. (Leased lines are dedicated and therefore more difficult for cyber crooks to compromise than the public Internet, but they can also be prohibitively expensive.)
By using VPN tunnels, highly distributed companies are able to provide relatively inexpensive IT continuity and security from a central location (such as Head Office) to branch offices, remote employees working from home or through mobile devices, and even to vendors and partners and your SYSPRO Support help desk.
Erasing geographical boundaries through a VPN promotes efficient workflow, providing remote access to relevant information, and allowing the company ERP to process documents and register transactions as they happen. In turn, this facilitates enterprise agility, a very important consideration in the ruthless global economy.
In Part 2 of this blog, we’ll talk more about VPN: How it works and what it can do for your company.
Recommended Interesting Reads: If you get Caught Using VPN UAE you will Face Fines