Sometimes it takes an unfortunate occurrence, initiated by malicious actors, to drive home the realization that we operate our businesses under the predatory gaze of thieves. For me, despite years of experience in risk identification, mitigation, and transference, that defining event came several weeks ago, when I found an email in my in-box from one of our senior execs:
Sanjay, please wire $xxx,xxx.00 to ABC Consulting today. Invoice attached.
Thanks, Maddie.
On the face of it, the request appeared legitimate. Maddie is well known to me, as is the consulting firm in question, and neither the nature nor the amount of the request was extraordinary. When I looked at the invoice, however, I knew immediately that something was wrong.
The first thing I did was contact Maddie, in the old-fashioned, inefficient, 20th-century manner, by knocking on her office door. Had she sent me this email? Maddie shook her head emphatically and my suspicions were confirmed. Her account had been hacked.
A few minutes later our head of IT had locked down Maddie’s email. That thwarted any future mischief, and gave us time to question and dig:
Had other malicious emails been sent from Maddie’s address? No – thankfully, we’d caught the intrusion in time.
Had anyone else’s email been compromised? Again, the answer was negative.
That was a relief, but there was no time to rest on our laurels. The incident response team was gathered, the Board notified, and our investigation began.
In the pre-IT world, manufacturers maintained an ‘air-gap’ between themselves and the outside world. Today, however, we have come to rely on IP-connected, enterprise-wide business systems to build and maintain competitive efficiencies. Given the pace of competition, and the realities of consumer-driven markets, manufacturers are rapidly pushing to implement systems, connect product lifecycles, incorporate mobile devices and build a digitally connected shop floor using, for example, the Internet of Things (IoT). With all of that burgeoning complexity, it’s no real surprise that manufacturers are attractive targets for cybercrime. The situation is made worse by the fact that cybercrime is generally low-risk but can deliver enormous payoffs in cash, IP, and other types of personal and company data.
How to manage the financial risks of cybercrime
As a CFO in 2020, I have a roster of duties and a breadth of mandate that might baffle my counterparts from a previous century. My job, beyond the mere crunching of numbers, is to drive innovation and complex analytics throughout the organization. And since innovation is intimately bound to technology, I am also responsible for identifying, mitigating, and transferring the risks of the IT systems we install.
Despite my intimate involvement with technology, it is not my job to mimic the skill sets of the CTO. As one would expect, it’s my job to approach the issue of cybercrime from a financial perspective. To that end, I create strategies that help me to identify, analyze and transfer the net financial risk1 of cybersecurity, and to calculate the ROI on our cybersecurity investments. From a manufacturing point of view, this means establishing a strategic approach to managing the financial risks of cybercrime, and embedding those risks into our existing risk-management framework.
To do that takes an integrative and wholistic approach. Firewalls and anti-virus programs are important, but cybercriminals are highly motivated and technically adept. They, like us, are constantly seeking a competitive edge. To rely on technology alone for your company’s wellbeing is to vastly underestimate your attackers. Thus, the ‘solution’ to cybersecurity is only partially technical. There are risks and appropriate responses in every department of a manufacturing concern, and to be robust, a strategic approach must involve data and observations from a wide variety of disciplines.
Using ERP as a tool to manage cybercrime
As a CFO, I rely on data as my primary weapon in the war against cybercrime. To that end, I gather data points from our ERP, and qualitative information from major stakeholders across the enterprise, including major stakeholders from IT, operations, regulatory, human resources, communications, supply chain, customer service and legal. It is possible, even probable, that every department has its own perspective and needs, and can shed valuable light on its particular concerns and vulnerabilities.
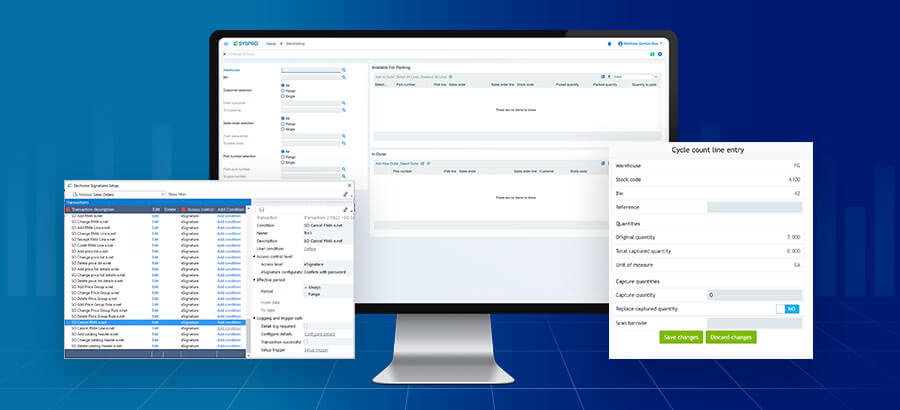
Although an improperly secured ERP can itself present vulnerabilities, it is without a doubt the most important tool at a CFO’s disposal. It provides a wholistic and granular view of the entire organization and allows me to gather data on a wide variety of potential vulnerabilities. It also performs a long list of essential cybersecurity functions, such as back-ups and user access control. SYSPRO, for example, provides role-based security, thus minimizing the potential for insider mischief.
Cybercrime caveats to bear in mind
There are three caveats, however, that I beg you to keep in mind.
- UPDATES!
- EMPLOYEE TRAINING – I hope this is a given. Not only is regular user training important for cybersecurity, it will also protect your ERP’s ROI, by helping to prevent the crippling effects of application erosion.
- UPDATES – I realize that I listed ‘updates’ twice, but updates are so important, and so often neglected, that I believe the repetition is warranted.
Only by collating and analyzing the full spectrum of data, with the help of both ERP and a full spectrum of major stakeholders, can a CFO begin to assess a company’s net financial risk. And without that initial calculation, or without sufficient confidence in that calculation, the mitigation and transference of cyber risk are likely to be insufficient or misdirected.
Key cybercrime statistics
- Worldwide spending on cybersecurity is forecasted to reach $133.7 billion in 2022. (Gartner)
- 62% of businesses experienced phishing and social engineering attacks in 2018. (Cybint Solutions)
- 68% of business leaders feel their cybersecurity risks are increasing. (Accenture)
- Only 5% of companies’ folders are properly protected, on average. (Varonis)
- Data breaches exposed 4.1 billion records in the first half of 2019. (RiskBased)
- 71% of breaches were financially motivated and 25% were motivated by espionage. (Verizon)
- 52% of breaches featured hacking, 28% involved malware and 32–33% included phishing or social engineering, respectively. (Verizon)