Walls and watchwords protected medieval castles against plundering masses. But firewalls and passwords cannot withstand cyber-attacks indefinitely. Ultimately, the safety of your cyber-city depends on the vigilance of its citizens. Slight paranoia also helps.
Heard the one about the bitcoin billionaire who cannot remember his crypto wallet’s password? It’s no joke. Just ask Stefan Tomas, a German programmer who helped develop the bitcoin platform a decade ago and received 7,002 freshly mined crypto coins for his effort. That’s the equivalent of R5,434-billion today. Yes, with a “b” for broke. In the absence of sense and sensibility, relying on technology to cover your own assets can be a bum mistake.
As an auditing clerk fresh out of university, I believed the simple shredder was the best defence against a breach of data security. You gathered the sensitive documents, put them through the shredder and forgot about it. If there was a chance that you might need to revisit the information, you filed it alpha-numerically in a fire-proof safe. Out of sight, out of mind, out of reach of those with evil in their hearts.
When cyber-security was in its infancy, it worked like our fire-proof safe. The techies built firewalls that they assured us would defend our perimeters against attacks from the evil outside.
Much like most castle walls, the concept of a perimeter has eroded with time. Many organisations no longer have a clearly defined “inside” or “outside”. Instead, they provide multiple access points to staff, customers and suppliers. Today, we focus on identity. Trust no one, inside or out, until you have verified their identity.
However, a mature cybersecurity model is as much a function of governance as it is about the technologies used to identify and validate these users or devices. If we see cybersecurity as “the guys in IT’s problem”, we run a genuine risk of becoming complacent as soon they install their latest security gizmos. But technical safeguards must be backed up by policies. And policies must be reinforced with compliance. Yet, even if we foster a culture of compliance, we remain exposed unless cyber governance falls within a broader framework of cyber awareness. Yep, human paranoia is the final fence.
What makes cybersecurity an agenda point for today’s CFO?
Enter Covid-19 and the subsequent mass movement of workforces to kitchen and garage offices. Payday for pirates. An Interpol report released in August 2020 shows a significant target shift in cyber-crime from individuals and small businesses to major corporations, governments, and critical infrastructure. CFOs might have been able to shy away from cybersecurity before, but no more. The biological pandemic of 2020 has paved the way for a cyber plague.
Cyber threats come at a hefty cost. Some of these costs – fines, ransom fees and revenue lost due to downtime – are clear to see. But the subsequent reputation damage may result in a loss of customer trust, drops in share prices and crumbling company valuations. It is up to the CFO and her finance department to put a number to that risk.
Furthermore, the CFO and the finance department hold a special place of honour in the hacker’s heart. Finance professionals are privy to the kinds of information that command some of the highest premiums on the dark web of stolen data. That makes you, dear finance professional, a prime target for all sorts of cyber thieves on phishing expeditions.
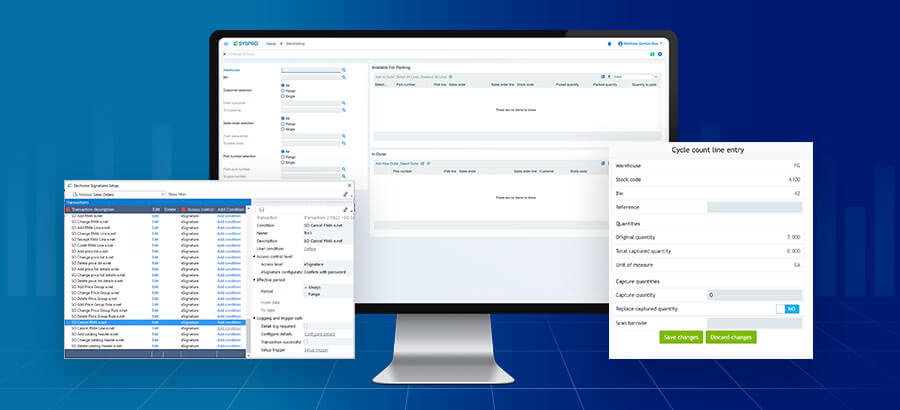
The finance department is very often the custodian of the company’s ERP system. The big drive for implementing an ERP system is its centralised functionality — a shared database that supports multiple functions and is used by many different business units. Most companies store highly sensitive data on their ERP systems, including financial results, manufacturing secrets, and bank details which help the business manage customers, employees, and suppliers. And this makes your ERP system a hot spot for cyber data theft.
Also, companies need their ERPs to function on the factory floor, in the distribution centre and across their retail outlets. That makes their ERPs bullseyes for distributed denial-of-service (DDoS) attacks.
Recently, two cyber-threat intelligence firms – Digital Shadows and Onapsis – conducted extensive research on ERP systems and identified several threats and vulnerabilities related to these systems. These threats have been considered significant enough for the United States Department of Homeland Security to warn against cyber-attacks on ERP systems.
Some mistakenly think that cybercrime is purely a technological risk and that techies and their tools should manage it. Not so. Cybercrime is a commercial risk and companies should address it focusing on three factors: technology, policy, and people.
That does not mean the CFO needs to understand the detail of the technical landscape when they lead the conversation on cybersecurity. For example, as a finance professional, you would not access the dark web (Or maybe let me rephrase: As a finance professional, please do not access the dark web!), but you need to appreciate the risks and the criminal opportunities it presents.
The focus of the CFO should be on implementing the policies that underpin the technology. Let’s get the basics right:
- Acceptable use: For what can employees use company equipment and for what not. Your company laptop isn’t much different from your company car. If you’re not allowed to use your company car to go on holiday, maybe you shouldn’t be allowed to use your company laptop to browse for holiday accommodation.
- Passwords: Rules covering the format and updating of passwords and their reuse. (No, madam, you cannot put your SYSPRO password on a sticky note on your computer monitor.)
- Bring Your Own Device (BYOD): How employees should use, connect, and encrypt personal devices they use for company business. Today the proliferation of Internet of Things (IoT) devices create a new mode of attack. Eavesdropping is no longer something a worried mother does from outside a teenager’s door. It is an actual technique used to retrieve communication between IoT objects.
- Email/communication: Acceptable use of email, social media, and telephone. That innocent-looking email attachment is still a viral vehicle for malicious code, even if it comes in the shape of a cuddly kitten meme from your granny.
Your company’s cybersecurity is only as strong as its weakest link, and every so often, that link is the people who work within your company. Their behaviour may create risk, either by sophisticated social engineering (such as spear phishing) or human error (such as losing a device). Only through education and awareness can we strengthen this last link. Give the hungry fish, and you feed them for a day. But teach them about phishing and they’ll be appropriately paranoid (and safer) for life.